Source-Based Entity Map — April 20, 2026
Details
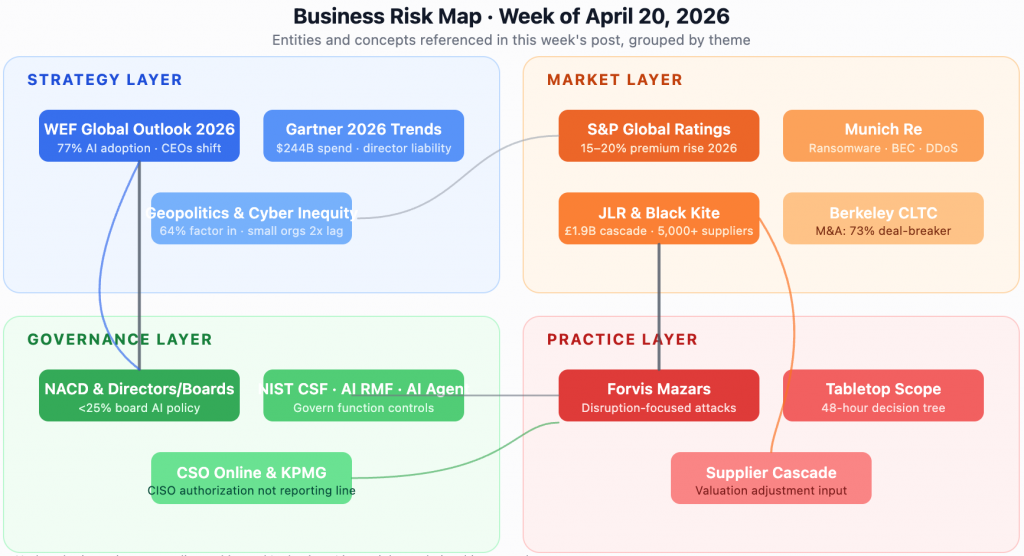
Business Risk & Executive Insights · Published Monday, April 20, 2026 Source-Based Entity Map · Week of April 20, 2026 Eight primary sources on the outside. Six cross-source convergences in the centre. WEF Outlook 2026804 leaders / 92 countries Gartner 2026top 6 trends (press release) S&P Ratings 2026via Industrial Cyber recap CSO OnlineGaillard · 16 Apr 2026 Directors & BoardsSharp/Sundaram · 16 Feb Berkeley CLTCM&A framework (2022) Industrial Cyber / BK136 breaches · 5.28 per Forvis Mazarswiper · 3 Apr 2026 Board & execliability3 sources AI / agentic AIWEF·Gartner·DB·Forvis4 sources Supply chainconcentration4 sources Geopolitics &nation-state3 sources Tabletop & IRresilience3 sources CISOauthority2 src Identity /control plane2 src Outer node = primary source document · Inner node = theme cited by 2+ sources · Edge weight = citation strength Source-based entity map: eight primary documents and the themes they converge on.
Deck: Cyber insurance rates are turning, acquirers are walking from deals, and cascading supply-chain incidents are now measured in billions. Governance of the IT and security function has not caught up to how boards now treat the risk.
Three data points published in the first four months of 2026 tell a coherent story for anyone sitting on a board, running a risk committee, or reporting into one.
The strategy layer
The World Economic Forum’s Global Cybersecurity Outlook 2026, built on survey data from more than 800 leaders across 92 countries, finds that 77% of organizations have now deployed AI inside their security operations, primarily for phishing detection, intrusion response, and user-behavior analytics. That adoption rate is running ahead of the governance scaffolding around it. More than half (54%) of respondents cite insufficient internal skills to deploy AI safely; 41% flag the need for human oversight as a primary constraint; 64% now explicitly factor geopolitical tension into their risk-mitigation strategy. The same report documents a widening “cyber inequity” gap: smaller organizations are roughly twice as likely as large enterprises to report insufficient resilience.
The headline from the WEF survey has been the shift in what CEOs list as their top concern, with cyber-enabled fraud overtaking ransomware. That framing is useful for CFOs but partial for IT and security leaders. The operational implication is different: the IT estate is being asked to absorb AI-era detection and response capability faster than it is being resourced to govern it. A CISO reading the WEF data honestly has to ask whether their organization’s AI-for-security adoption is genuinely reducing analyst workload or creating a new class of decisions no one is accountable for.
The market layer
S&P Global Ratings’ 2026 Cyber Insurance Market Outlook forecasts a 15 to 20 percent premium increase in 2026, ending three consecutive years of rate softening. Premiums had fallen 22% from their 2022 peak and another 6% in 2025. The turn is partly a matter of underwriting discipline. Munich Re’s 2026 outlook identifies ransomware, business email compromise, data breach, and DDoS as the four categories still driving claim severity. It is also partly the market pricing in risks such as AI-enabled fraud and cascading supplier incidents that were not visible in the prior cycle.
Case study: the UK’s Cyber Monitoring Centre categorised Jaguar Land Rover’s August 2025 cyberattack as a Category 3 systemic event with an estimated £1.9 billion UK financial impact and more than 5,000 UK organisations affected, making it the most economically damaging cyber event to hit the UK to date. The incident produced a five-week production halt and prompted a £1.5 billion UK government loan guarantee. Black Kite’s 2026 third-party breach report frames the cascade dynamic more broadly: 136 disclosed third-party breaches produced more than 26,000 downstream victims, an average of 5.28 downstream organisations per incident. Attacks that clear £1 billion in quantified downstream cost become reference events for underwriters, regulators, and acquirers simultaneously.
Corporate-development teams are already moving. Forescout’s benchmark “Role of Cybersecurity in M&A Diligence” survey of 2,700 IT and business decision-makers found that 73% of executives consider an undisclosed data breach an immediate deal-breaker and 53% report that a critical cyber issue has jeopardized a deal in progress. Berkeley CLTC’s Moving Left and Right framework provides the diligence scaffolding acquirers are now applying on top of those signals. When insurance, acquirers, and regulators price a risk in parallel, boards typically follow.
The governance layer, where the gap shows
The National Association of Corporate Directors reports that fewer than 25% of boards have a structured, board-approved AI policy, and only 39% of Fortune 100 companies disclose any form of board AI oversight, despite more than 88% of organizations using AI in at least one business function. NIST’s February 2026 AI Agent standards initiative is attempting to close the vacuum, but the governance lag is the lag.
A parallel piece from CSO Online and a 2026 KPMG Boardroom Strategy note both reframe the long-running “who does the CISO report to?” question. The real question, they argue, is not reporting line but decision rights: what is the CISO authorized to stop, start, or reshape? When authority lives only in IT, cyber remains a recommendation function. When authority is documented at the enterprise level, cyber becomes the decision-making function boards increasingly expect it to be.
Forvis Mazars’ April 2026 operational-resilience research adds a fourth analytic frame. A rising class of attacks is designed not to steal or encrypt but to degrade operations, often via misuse of legitimate administrative access. Traditional incident-response playbooks do not cover these scenarios well. The firm recommends expanding tabletop scope to rehearse business-continuity decisions executives would otherwise make under duress.
A fifth frame, close to how sitting CISOs use this kind of news day-to-day, came from the US Coast Guard’s Cybersecurity in the Marine Transportation System rule and Dark Reading’s April 2026 analysis of its implications. The rule codifies a designated cybersecurity officer, a written cybersecurity plan, mandatory training, and a specific set of account-security controls: multi-factor authentication, least-privilege on privileged accounts, default password rotation, minimum password strength, and automatic lockout on repeated failed login attempts. Compliance dates run through July 2027. The rule is maritime, but the control set is the one enterprise CISOs have been pushing internally for years. A sector regulator codifying the same programme is leverage: the CISO outside maritime now has a parallel-authority citation for the same board conversation. Reading new sector regulations for their design logic, not their compliance checklist, is a high-return use of a CISO’s week.
What to do
For boards, risk committees, and CEOs using Q2 planning cycles:
- Align authority with accountability. Before the next quarterly review, document in writing, at the enterprise level, what the CISO is authorized to decide unilaterally, what requires CEO concurrence, and what requires a board vote. NIST CSF Govern (GV.RR) is the control reference.
- Ratify an AI policy at board level. Do not accept “management is drafting one” as a Q2 answer. Anchor it on the NIST AI RMF’s Govern function and require disclosure in the next proxy.
- Re-baseline the cyber insurance conversation. Assume a 15 to 20 percent premium increase. Use the renewal window to negotiate scope (ransomware extortion, business interruption, contingent BI), not just rate.
- Expand tabletop scope to disruption-focused scenarios. Rehearse a 48-hour executive decision tree for an incident that looks like an outage rather than a breach. Forvis Mazars’ framing is a useful template.
- Put supplier cascade on the acquisition checklist. Any target whose top-10 suppliers are not themselves cyber-attested should carry a valuation adjustment, not a post-close remediation plan.
- Read new sector regulations as CISO template, not compliance burden. When a regulator outside your sector codifies a specific control set, pull the list, map it against your current posture, and bring the gaps to your next board cycle. The Coast Guard MTS rule is the current worked example. NIST CSF Protect and Govern are the mapping references.
The market has moved. The next 90 days determine whether governance moves with it.
Sources
- World Economic Forum: Global Cybersecurity Outlook 2026
- Industrial Cyber: S&P Global sees cyber insurance premiums climbing 15–20% in 2026 (recap of S&P Ratings 2026 Outlook)
- Munich Re: Cyber insurance risks and trends 2026
- Cyber Monitoring Centre: Statement on the Jaguar Land Rover cyber incident (Oct 22, 2025)
- Industrial Cyber: Black Kite 2026 third-party breach report (cascade dynamics)
- Forescout: The Role of Cybersecurity in Mergers & Acquisitions Diligence (2,700 ITDM/BDM survey)
- Berkeley CLTC: Moving Left and Right (Cyber in M&A Diligence framework)
- Computer Weekly: Global cyber spend will top $200bn in 2025, rising to ~$240B in 2026 (Gartner forecast recap)
- Directors & Boards: AI Adoption and Cybersecurity Oversight (NACD data)
- NIST AI Risk Management Framework
- CSO Online: The endless CISO reporting-line debate
- Forvis Mazars: Disruption-focused cyberattacks and operational resilience
- Dark Reading: Coast Guard’s Cybersecurity Rules Offers Lessons for CISOs
- US Coast Guard: Cyber Regulations Fact Sheet (Marine Transportation System)